Understanding VPN Logging Policies: Claims, Practices, and Gaps
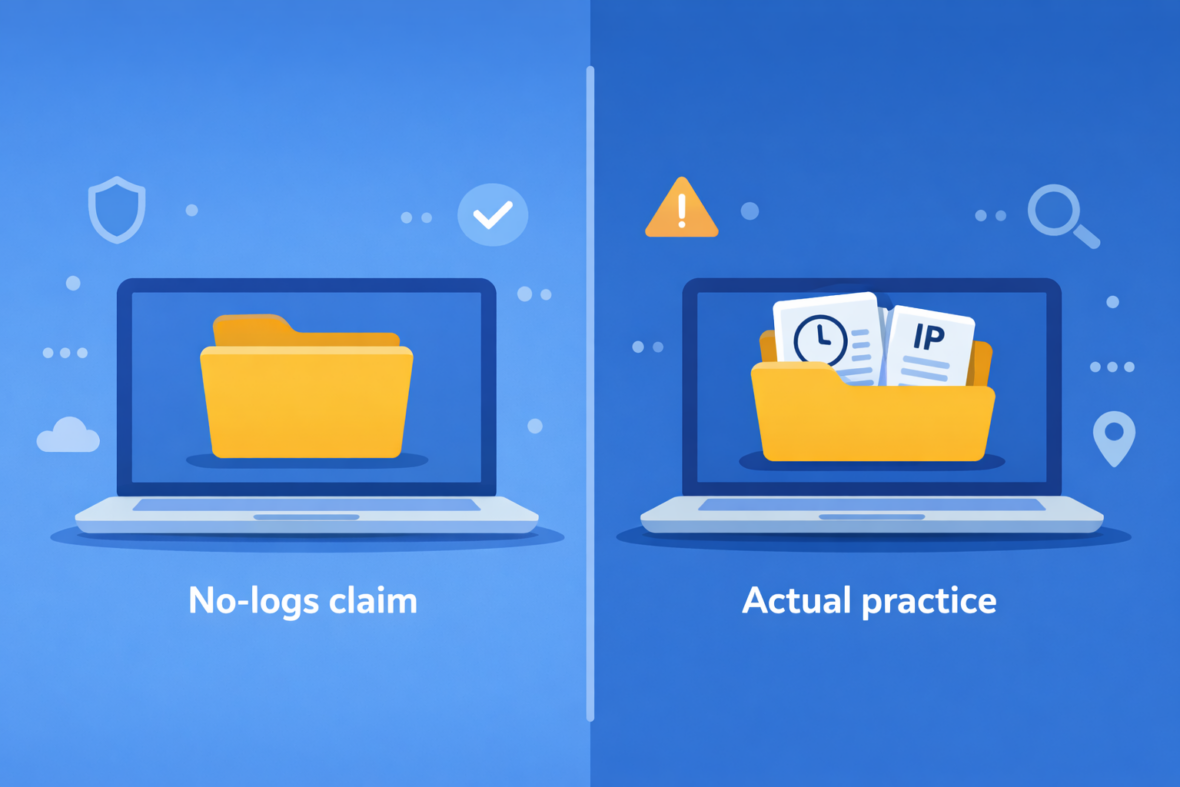
VPN logging policies can be confusing because the word “logs” is used broadly and often without clear definitions. Many providers advertise “no-logs,” but the details behind that claim can vary significantly depending on what data is counted as a log and how long it is retained.
This guide explains what VPN “logging” typically means, which log types matter most for privacy, and how to read policy language more critically. Where information is unclear or missing, it is reasonable to treat it as Not specified rather than assume nothing is collected.
What “Logging” Means in the Context of VPN Services
In the context of VPN services, “logging” generally refers to any record a provider creates or stores about VPN use. Logs can include activity-related information (such as websites or DNS requests) as well as technical metadata (such as connection timestamps, server selection, or IP address handling). Not all logs carry the same privacy implications, which is why the category and retention details matter.
It can help to distinguish between data that exists briefly while a service is running and data that is stored and retrievable later. Many systems generate operational data by default, even if it is short-lived, aggregated, or not tied to browsing activity. Whether that data is retained, how it is protected, and whether it can be linked to an account are the more meaningful questions.
| Temporary operational data | information processed in real time to route traffic or keep the service stable. |
|---|---|
| Stored records | data retained in a way that can be accessed later (for example, for support, billing, or compliance). |
Common Types of VPN Logs (And Why the Distinction Matters)
When VPN providers talk about logs, they may be referring to very different types of data. Some categories could reveal meaningful patterns if retained with identifiers, while others are primarily operational or administrative. Understanding the difference helps you interpret “no-logs” claims more accurately.
- Connection timestamps Records of when a VPN session started or ended. If stored alongside identifiers, timestamps can narrow down a time window for activity, depending on what else is retained.
- Bandwidth or usage totals Information about how much data was transferred. Some providers describe this as aggregated or anonymous, but the privacy impact depends on whether it is linked to an account or a specific session.
- IP address handling Details about source IP addresses (your real IP) and assigned VPN IP addresses. Policies may say this data is not stored, stored temporarily, or may not specify retention clearly.
- Account and diagnostic data Account identifiers (email, subscription status) and diagnostics (crash reports, app errors). These may not reveal browsing activity directly, but they can still identify a user.
Because “logs” can describe multiple categories, a policy that says “we do not log” may only be referring to one type of data. The practical meaning depends on whether other records exist and how they are described.
What VPN Providers Usually Mean by “No-Logs”
“No-logs” is often used as a shorthand claim that a VPN does not record user browsing activity while connected. In many privacy policies, this typically means the provider says it does not store the contents of traffic, a history of visited sites, or DNS queries in a way that can be reviewed later.
However, policy language can be conditional or incomplete. Some statements focus on “activity logs” while allowing limited “service” or “connection” data for operations, troubleshooting, or abuse prevention. When “no-logs” is not followed by explicit data categories and retention details, it can be difficult to understand what is truly excluded.
| “May collect” / “may retain” | suggests practices can vary by scenario or product. |
|---|---|
| “For troubleshooting” | may indicate diagnostic data or support logs are kept. |
| “To prevent abuse” | may imply short-term or limited metadata retention. |
| “Anonymous statistics” | may be meaningful, but the included fields are sometimes Not specified. |
❗ Important note
“No-logs” is not a universal technical standard. A provider may avoid storing browsing activity while still retaining some account or operational data, depending on how the policy defines logs.
What Is Often Not Clearly Disclosed in Logging Policies
Even detailed privacy policies often leave gaps around edge cases and operational realities. This does not automatically indicate extensive logging, but it can limit how confidently you can interpret a claim, especially when key terms are not defined.
One common ambiguity involves short-lived or aggregated data. A provider may state it does not store certain information “long term” without clarifying what happens during connection establishment, how long operational records persist, or whether identifiers are removed. Without clear retention periods, privacy impact is harder to assess.
| Temporary or aggregated logs | short-term records for stability, routing, or monitoring, sometimes described without timeframes. |
|---|---|
| Abuse-prevention logging | limited records to address spam, fraud, or unusual usage, often with minimal detail. |
| Third-party infrastructure logs | hosting providers, analytics tools, or protection services may generate their own logs. |
| Unmentioned categories | if a policy does not address a data type, it is reasonable to treat it as Not specified. |
These gaps are one reason it can be misleading to compare VPNs only by headline claims. The absence of disclosure does not prove the absence of logging; it only shows that details are not publicly documented.
Jurisdiction, Legal Obligations, and Their Impact on Logging
VPN providers operate within legal frameworks that can affect what they are allowed to collect, retain, or disclose. Jurisdiction can matter both where the company is registered and where servers or supporting infrastructure are located. Even when a provider states a strong privacy position, legal obligations may shape how it responds to requests for data.
In some places, data retention rules apply broadly to communications services, while in others VPNs are not explicitly addressed. This means two providers with similar policies may face different constraints depending on local law and enforcement. Public information can also be incomplete or hard to compare across regions.
| Company jurisdiction | Determines which national laws and courts can issue data requests or subpoenas |
|---|---|
| Data retention requirements | May require certain metadata to be stored for a defined period, depending on local law |
| Law enforcement requests | Can compel disclosure of data that is available, even if limited or temporary |
| Cross-border infrastructure | Servers in different countries may be subject to different local regulations |
Jurisdiction is best viewed as one part of the overall picture, alongside policy clarity and transparency signals, rather than a standalone measure of privacy.
Why Logging Policies Can Change Over Time
VPN logging policies can change as products evolve and companies update their infrastructure. New features, new apps, and changes to how servers are managed can alter what data is processed or stored, even if the headline “no-logs” claim remains similar.
Ownership changes are another common reason for updates. When a VPN changes hands, internal processes, compliance priorities, or technical operations may shift. Even if the brand remains the same, backend practices can evolve in ways that affect data handling.
For readers, this is a reminder that older summaries or archived policy versions may not reflect current practice. When privacy is a priority, checking the most recent policy text and update date is usually more reliable than relying on past claims.
How to Read a VPN Privacy Policy Critically
VPN privacy policies are often written as legal documents rather than user guides. Reading them critically does not require legal expertise, but it does require attention to specific wording, missing details, and how claims are framed across different sections.
- Find explicit data categories Look for clear lists of what is and is not collected (for example, activity data, connection metadata, account data, and diagnostics).
- Check retention timelines If a policy uses phrases like “temporarily” or “as needed,” look for timeframes. If none are provided, treat retention as undefined.
- Identify conditional language Wording such as “may collect” or “may retain” can signal that practices depend on circumstances or product variations.
- Note what is not mentioned If a category (like DNS handling or IP address retention) is not addressed, treat it as Not specified rather than assume it is excluded.
A privacy policy can help you compare stated commitments, but it does not provide complete visibility into internal systems. It is most useful when combined with transparency reports, audit summaries (where available), and an understanding that implementations can differ between providers.
Key Takeaway: Understanding the Limits of “No-Logs”
Logging policies describe what a provider says it records, but they rarely offer full visibility into how every internal system behaves in every situation. Clear, specific wording can improve understanding, while vague language and missing retention details should be treated cautiously.
In practice, “no-logs” works best as a starting label for comparison — not as definitive proof of how a VPN operates. The most useful approach is to check which data categories are addressed, whether retention is clearly described, and what remains Not specified.
💡 Good to know
If you are comparing providers, prioritize policies that name specific data categories and retention periods over broad “no-logs” slogans with limited detail.
FAQs: VPN Logging Policies
-
Does “no-logs” mean a VPN keeps no data at all?
Not usually. Many providers still keep account-related data and may process limited technical data needed to run the service. The privacy impact depends on what is stored, how long it is retained, and whether records can be linked to an individual user.
-
Are temporary or in-memory logs still considered logs?
Temporary data is often treated differently from stored logs, but the practical impact depends on whether it is retained, whether identifiers are included, and whether retention timeframes are clearly described. If those details are not provided, they may be considered Not specified.
-
Do “no-logs” policies usually cover DNS queries?
It varies. Some policies explicitly say DNS queries are not stored, while others only discuss “activity logs” in broad terms. If DNS handling is not mentioned, it is safer to treat that detail as Not specified.
-
Do audits prove that a VPN keeps no logs?
Audits can increase confidence by reviewing specific systems at a point in time, but scope and frequency vary. They typically do not provide continuous oversight or guarantee how things will work after product or infrastructure changes.
-
Can legal obligations override a VPN’s stated policy?
Depending on jurisdiction, a provider may be required to disclose data that is available or comply with certain legal requests. What this means in practice can vary by local law and how requests are handled.
-
Why do some VPN policies use vague language?
Privacy policies are legal documents and often include flexible wording to cover multiple scenarios. Vague terms may reflect operational uncertainty, evolving systems, or the fact that certain details are not publicly documented.
